In recent months, the keyword “thejavasea me leaks aio tlp287” has gained attention across search engines, online forums, and blog discussions. Many internet users are curious about what this phrase means, why it is trending, and whether it represents a genuine cybersecurity issue or simply another example of viral leak culture. While some online sources describe it as a data bundle or archive, the topic is best understood through the lens of digital safety, online ethics, and the evolving landscape of information security.
This article explores the background, potential meaning, risks, and wider implications associated with thejavasea me leaks aio tlp287 — focusing on awareness rather than promotion.
The Rise of Leak-Related Keywords Online
The internet has always been a space where curiosity spreads quickly. Whenever a mysterious keyword appears — especially one connected to “leaks” — it tends to attract attention from both tech enthusiasts and everyday users. Over the past decade, leak culture has grown because of the demand for exclusive content, early releases, or access to restricted information.
However, many cybersecurity professionals warn that not every trending keyword represents something legitimate or trustworthy. Often, leak-related search terms circulate because of speculation, rumors, or attempts to lure users toward unsafe downloads.
The phrase thejavasea me leaks aio tlp287 seems to follow this pattern. Rather than being widely verified by major cybersecurity organizations, most discussions appear on smaller blogs or forums, which makes it important to approach the topic carefully and critically.
What People Mean by “thejavasea me leaks aio tlp287”
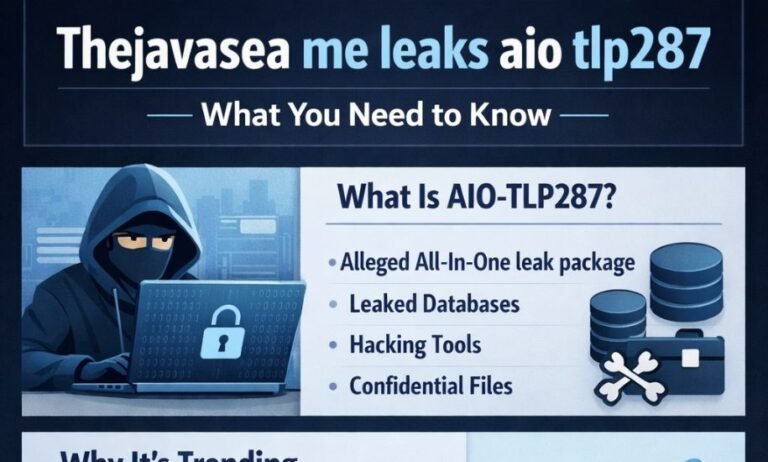
Based on various online discussions, the term appears to be a combination of three parts:
1. thejavasea me – Allegedly a website or platform discussed in leak communities. It is often described as a place where bundled digital content is shared or referenced.
2. AIO – Commonly stands for “All-In-One.” In internet culture, this usually refers to a collection of multiple files or tools packaged together.
3. TLP287 – Some bloggers suggest this may be a labeling system or internal identifier connected to a specific bundle or dataset.
Together, the phrase suggests a large compilation of files being discussed or circulated online. However, it’s important to understand that detailed information about the exact contents is unclear and often speculative.
The Culture Behind AIO Bundles
All-in-one packages have existed for years across many online communities. Sometimes they contain legitimate resources, such as software collections or learning materials. In other cases, they are linked to unauthorized distributions, which raises ethical and legal concerns.
The popularity of AIO bundles comes from convenience. Instead of downloading individual items separately, users receive a single archive that promises everything at once. Unfortunately, this convenience is also what makes such bundles risky.
Cybersecurity experts frequently warn that large bundled files can hide malicious content. Because users don’t always know what’s inside, they may unknowingly expose their devices to threats.
Why the Keyword Became Popular
Several factors likely contributed to the sudden attention around thejavasea me leaks aio tlp287:
- Curiosity about exclusive or hidden content
- Discussions spreading through online communities
- SEO-focused blog posts analyzing trending leak terms
- Growing public interest in cybersecurity topics
When a keyword appears repeatedly across search engines, people often assume it represents something major. In reality, online trends sometimes grow simply because many websites write about the same topic, creating a cycle of visibility.
Possible Contents Mentioned in Online Discussions
Although no verified public inventory exists, blogs discussing this keyword often speculate that such bundles may include:
- datasets or digital archives
- scripts or automation tools
- software files or experimental builds
- documents shared without official authorization
It is essential to emphasize that these descriptions are based on online commentary rather than confirmed sources. Because of this uncertainty, readers should treat claims about the contents with caution.
Cybersecurity Risks Associated With Leak Bundles
One of the most important aspects of this topic is the potential danger involved. Cybersecurity analysts consistently highlight several risks when dealing with unknown leak packages.
Malware and Hidden Threats
Files shared through unofficial channels can contain trojans, spyware, or ransomware. Even if a bundle appears harmless, hidden code may run silently in the background.
Phishing and Fake Download Pages
Some websites use trending keywords like thejavasea me leaks aio tlp287 to attract traffic and redirect users to suspicious links. These pages may request personal data or encourage unsafe downloads.
Data Privacy Concerns
Accessing leaked material can expose users to legal risks and ethical dilemmas. Many countries enforce strict laws regarding unauthorized distribution of private or copyrighted content.
Legal and Ethical Considerations
Beyond technical risks, there are also legal issues surrounding leak-related content. Intellectual property rights, privacy laws, and cybersecurity regulations differ across regions, but many governments treat unauthorized data distribution seriously.
From an ethical perspective, the rise of leak culture raises questions about digital responsibility. Even when users are curious, engaging with unverified sources can contribute to the spread of harmful content.
A safer approach is to treat such keywords as informational topics rather than invitations to explore unknown files.
How Cybersecurity Experts View Trends Like This
Professionals in the cybersecurity field often see viral leak keywords as reminders of how quickly information spreads online. Whether or not thejavasea me leaks aio tlp287 represents a real dataset, the attention it receives highlights a broader issue: many internet users remain vulnerable to curiosity-driven risks.
Experts recommend several best practices:
- Avoid downloading files from unknown sources
- Use strong, unique passwords
- Keep antivirus and system updates active
- Verify information through trusted cybersecurity news outlets
By focusing on awareness rather than participation, readers can stay informed without putting their devices or personal data at risk.
The Role of Blogs and SEO in Amplifying Trends
Another interesting aspect of this keyword is how blog websites contribute to its visibility. When writers publish articles about trending terms, search engines begin associating those keywords with informational content. As more blogs discuss the topic, it appears more frequently in search results, which encourages additional curiosity.
This cycle demonstrates the power of SEO in shaping online discussions. Even a relatively obscure phrase can become widely searched if enough content is created around it.
For readers, this means it is always wise to evaluate sources critically. Not every trending keyword reflects a confirmed event — sometimes it simply reflects online conversation.
Lessons Internet Users Can Learn From This Topic
The attention surrounding thejavasea me leaks aio tlp287 offers several important lessons:
- Curiosity should be balanced with caution.
Trending keywords often attract clicks, but safety should always come first. - Not all online information is verified.
Blogs may discuss theories or rumors, so cross-checking information is essential. - Cybersecurity awareness matters more than ever.
As digital threats evolve, understanding risks helps users make better decisions online.
Looking at the Bigger Picture
Whether thejavasea me leaks aio tlp287 represents a real archive or simply an internet trend, it reflects how modern online culture blends curiosity, technology, and risk. The internet moves fast, and new topics appear every day. Some fade quickly, while others become part of broader conversations about privacy and digital ethics.
Instead of focusing solely on the mystery behind such keywords, readers can use them as opportunities to learn about online safety and responsible browsing habits.
Final Thoughts
The growing search interest in thejavasea me leaks aio tlp287 shows how quickly niche topics can reach mainstream attention. While many blogs attempt to explain or analyze the term, the most important takeaway is awareness. Unknown leak bundles and unofficial downloads often carry more risks than rewards.
If you enjoy reading about technology trends, cybersecurity insights, and internet culture, platforms like angliatimes aim to explore these topics from an informational and responsible perspective. By focusing on education rather than hype, readers can stay updated without exposing themselves to unnecessary digital threats. Articles published on angliatimes continue to highlight the importance of safe browsing, ethical online behavior, and understanding how viral keywords shape modern web discussions.